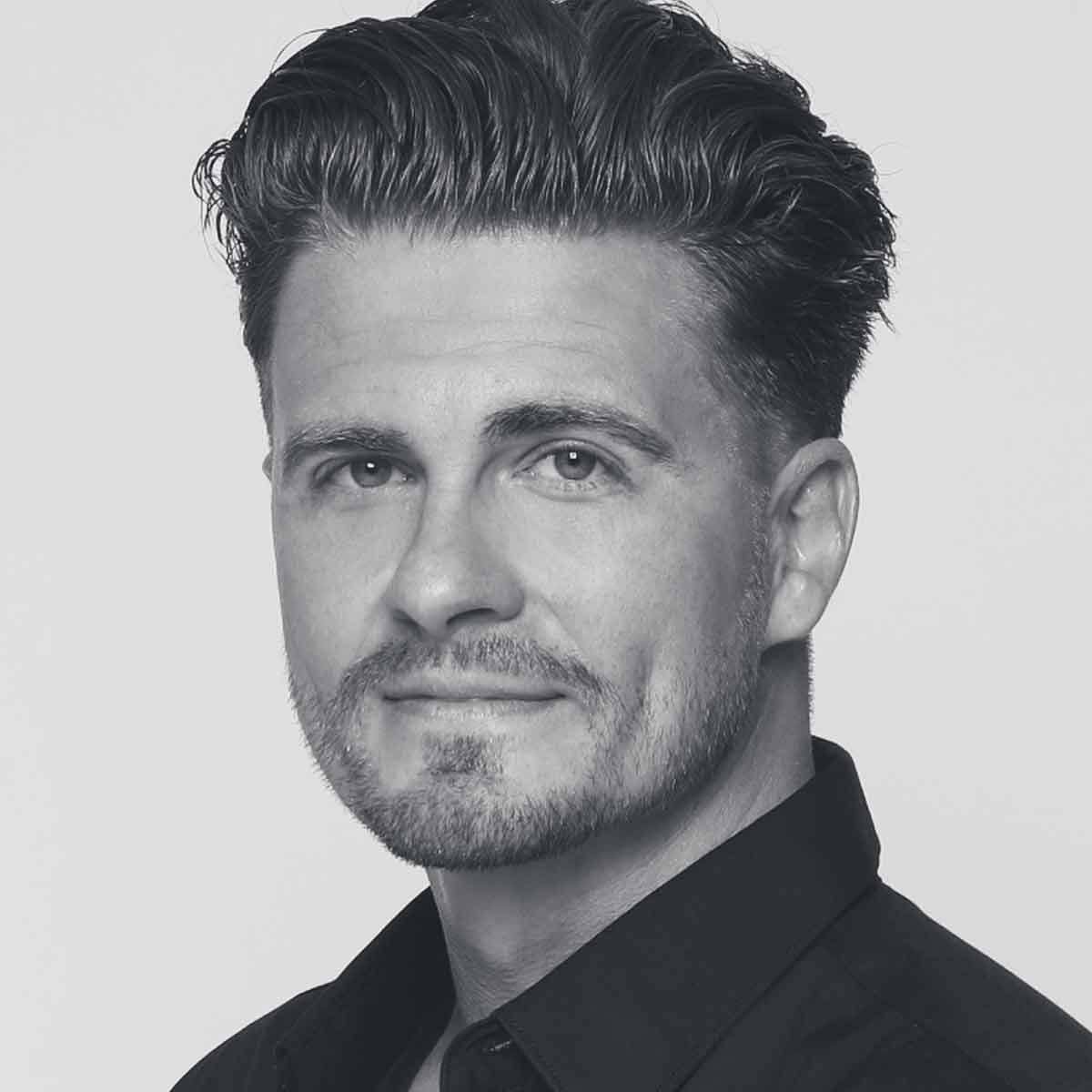
Tanmay Bakshi is a 16-year-old Canadian author, AI and ML Systems Architect, TED & Keynote speaker, Google Developer Expert for Machine Learning, and IBM Developer Advocate. He has addressed over 200,000 executives, students, and developers worldwide at conferences, universities, financial institutions, and international companies. The United Nations, Linux Foundation, Apple, SAP, IBM, KPMG, Microsoft, and Walmart are a few of the organizations he has keynoted for.
Tanmay has been covered in the media, being featured in the Toronto Star, on the front page of The Vancouver Sun, pictured on stage doing what he loves to do - sharing his knowledge with the world, in Forbes and CNBC, as well as in Bloomberg Businessweek as a Young Entrepreneur, in The New York Times, and The Wall Street Journal, just to name a few.
His YouTube channel called “Tanmay Teaches” is where he shares his research and knowledge with audiences of all ages, and is the host of the live series “Tech Life Skills with Tanmay”. He has had the honour of being the recipient of the Life Mentor Award by the Hon. Lt. Governor of Manitoba, Twilio Doer Award, Knowledge Ambassador Award, and Global Goodwill Ambassador at LinkedIn.
He has developed machine learning powered systems, such as "Heart ID", a deep neural network based Electrocardiogram-based identification system, which won HPCWire's Readers’ Choice Award for Best Use of High Performance Data Analytics & Artificial Intelligence. He's also worked on lower level software, like an ultra low-latency call tracer utility that can scale to trillions of function calls, and is powered by LLVM, for the IBM Db2 codebase.