Henning Harbs
Cybersecurity for Software Defined Vehicles
#1about 2 minutes
The automotive industry's shift to software-defined vehicles
The transition from hardware-centric cars to complex, connected software-defined vehicles introduces new capabilities and challenges.
#2about 3 minutes
Understanding the UNECE R155 cybersecurity regulation
The UNECE R155 regulation mandates a certified cybersecurity management system (CSMS) for all new vehicles, impacting the entire supply chain.
#3about 3 minutes
Managing security over the entire vehicle lifecycle
Vehicle cybersecurity must be maintained for over a decade, requiring continuous monitoring, incident response, and robust over-the-air update capabilities.
#4about 3 minutes
Volkswagen's approach to in-vehicle network security
Volkswagen's security technology kit uses a secure service-oriented architecture (SOA) with TLS to protect in-vehicle communication between ECUs.
#5about 2 minutes
The OBD port as a physical attack vector
The standardized On-Board Diagnostics (OBD) port creates a significant physical vulnerability, comparable to an unsecured USB port on a laptop.
#6about 4 minutes
Real-world examples of modern car hacking techniques
Several real-world examples, including CAN injection, key fob brute-forcing, and relay attacks, demonstrate common vehicle vulnerabilities.
#7about 1 minute
Defending against attacks and the future of automotive security
Ultra-wideband (UWB) technology prevents relay attacks by measuring signal time-of-flight, representing a paradigm shift towards proactive, long-term cybersecurity management.
#8about 3 minutes
Q&A on securing CAN bus and future architectures
The discussion covers securing legacy systems like CAN bus, the role of open standards like AUTOSAR, and the importance of domain separation in future vehicle architectures.
Related jobs
Jobs that call for the skills explored in this talk.
IGEL Technology GmbH
Bremen, Germany
Senior
Java
IT Security
VECTOR Informatik
Stuttgart, Germany
Senior
Java
IT Security
CARIAD
Berlin, Germany
Junior
Intermediate
Python
C++
+1
Matching moments
07:51 MIN
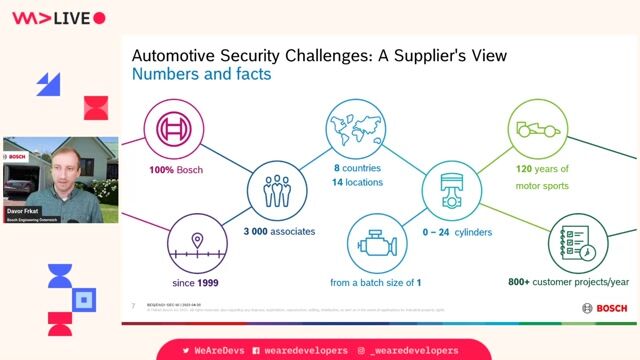
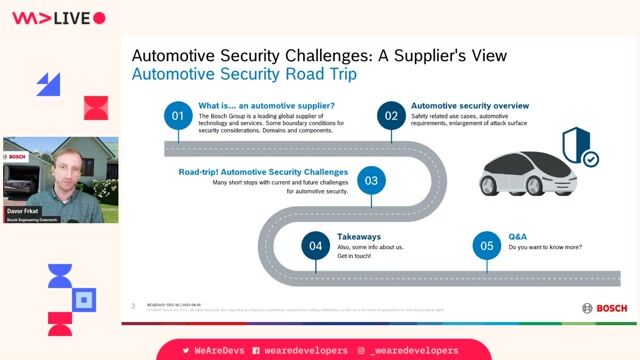
An overview of the automotive security landscape
Automotive Security Challenges: A Supplier's View
04:00 MIN
Exploring the security vulnerabilities of connected cars
Using all the HTML, Running State of the Browser and "Modern" is Rubbish

03:18 MIN
The role of security in specialized vehicle projects
Cyber Security: Small, and Large!

06:39 MIN
New threats from modern vehicle E/E architectures
Automotive Security Challenges: A Supplier's View

04:50 MIN
Security challenges of autonomous driving and forensics
Automotive Security Challenges: A Supplier's View
03:43 MIN
Modern cybersecurity challenges for developers
Cyber Security: Small, and Large!

05:19 MIN
Adhering to automotive security standards and regulations
Automotive Security Challenges: A Supplier's View

05:24 MIN
Vulnerabilities in keyless entry and vehicle data
Cyber Security: Small, and Large!
Featured Partners
Related Videos
 37:32
37:32Cyber Security: Small, and Large!
Martin Schmiedecker
 27:32
27:32Security Pitfalls for Software Engineers
Jasmin Azemović
 41:03
41:03The best of two worlds - Bringing enterprise-grade Linux to the vehicle
Joachim Werner
 1:54:28
1:54:28What makes Cybersecurity different for critical infrastructure?
Kurt Eder
 58:59
58:59Automotive Security Challenges: A Supplier's View
Davor Frkat
 29:47
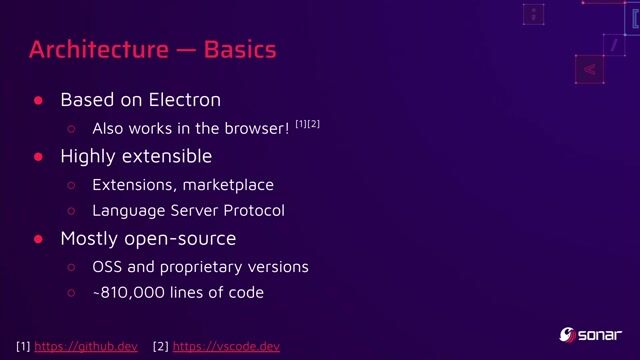
29:47You click, you lose: a practical look at VSCode's security
Thomas Chauchefoin & Paul Gerste
 1:58:48
1:58:48Software Security 101: Secure Coding Basics
Thomas Konrad
 21:49
21:49A Hitchhikers Guide to Container Security - Automotive Edition 2024
Reinhard Kugler
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.

Bertrandt AG
Hamburg, Germany
C++

Bertrandt AG
Taufkirchen, Germany
C++

Bertrandt AG
Manching, Germany
C++

Prognum Automotive GmbH
Ulm, Germany
Remote
C++



Prognum Automotive GmbH
Ulm, Germany
Remote
Burp Suite


Mercedes-Benz Tech Innovation GmbH
Stuttgart, Germany
Remote
Go
GIT
Bash
Linux
+4