Antonio de Mello & Amine Abed
The attacker's footprint
#1about 10 minutes
Defining key cybersecurity tools and terminology
An overview of essential information security concepts and tools is provided, including nmap, Burp Suite, IDOR, LFI, and SIEM platforms.
#2about 16 minutes
Performing reconnaissance with an nmap port scan
The initial attack phase begins with an nmap scan to discover open ports and services, identifying potential web applications and an Apache server.
#3about 11 minutes
Gaining initial access with default credentials
After failed SQL injection attempts, access is gained by logging in with common default credentials and a path disclosure vulnerability is found via a malformed JSON.
#4about 13 minutes
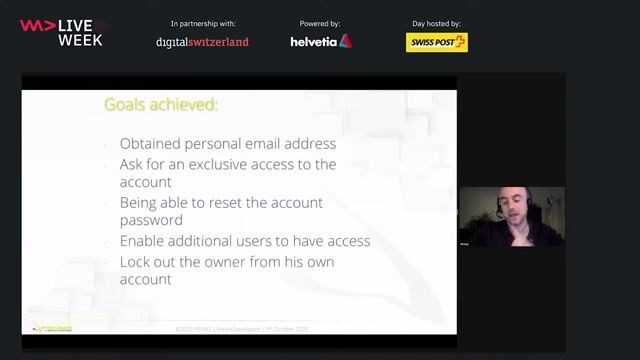
Exploiting broken access control with cookie tampering
A base64-encoded cookie is manipulated to access another organization's data, and fuzzing reveals a hidden admin parameter to view sensitive information.
#5about 10 minutes
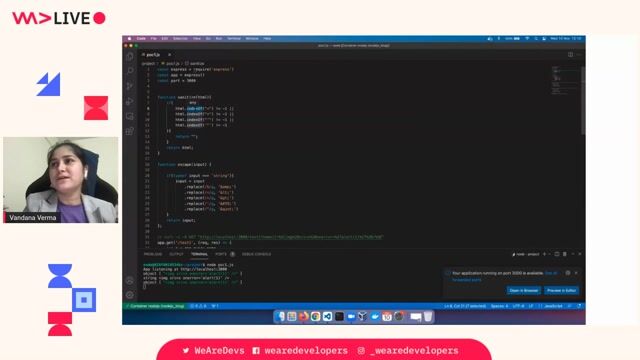
Reading sensitive files with a path traversal exploit
A known path traversal vulnerability in the Apache server is exploited to read the `/etc/passwd` file and a sensitive configuration file containing credentials.
#6about 1 minute
Achieving remote access via SSH with guessed credentials
Using the leaked username, the password from the configuration file is modified by incrementing the year to successfully log into the server via SSH.
#7about 21 minutes
Analyzing API logs to trace the attacker's steps
The defender analyzes API logs to identify failed SQL injection attempts, a successful login, parameter fuzzing, and cookie manipulation by observing response codes and body sizes.
#8about 15 minutes
Correlating web server and authentication logs
Apache and authentication logs are examined to find evidence of the nmap scan, the path traversal exploit, and the final successful SSH login after several failed attempts.
#9about 13 minutes
Demonstrating a SIEM for automated threat detection
A Security Information and Event Management (SIEM) tool is shown to automatically detect and flag suspicious activity, such as the nmap user agent, in real-time.
#10about 18 minutes
Summarizing vulnerabilities and key security recommendations
The workshop concludes with a summary of the attack chain and provides key recommendations for developers and defenders, such as patch management and maintaining high-quality logs.
Related jobs
Jobs that call for the skills explored in this talk.
Information Security Officer - Part-time (w/m/d)
aedifion GmbH
Köln, Germany
€30-45K
Intermediate
Network Security
Security Architecture
+1
Senior Fullstack Engineer – Angular/.Net (f/m/d)
Apaleo
München, Germany
Remote
€65-85K
Senior
JavaScript
.NET
+2
Matching moments
20:34 MIN
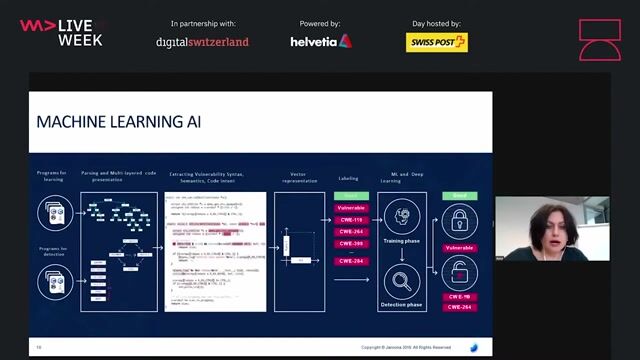
Applying security tools in test and delivery phases
Securing Your Web Application Pipeline From Intruders

14:17 MIN
Hands-on security training for developers
How GitHub secures open source

08:22 MIN
How attackers exploit developers and packages
Vue3 practical development

08:16 MIN
Common attacks targeting software developers
Vulnerable VS Code extensions are now at your front door
07:52 MIN
A practical demonstration of exploiting IDOR vulnerabilities
How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
04:37 MIN
Examining high-impact path traversal exploits in the wild
Hack-Proof The Node.js runtime: The Mechanics and Defense of Path Traversal Attacks
41:48 MIN
Live hack: Recreating the Apache Struts vulnerability
Stranger Danger: Your Java Attack Surface Just Got Bigger
28:11 MIN
Understanding the complete social engineering attack lifecycle
Getting under the skin: The Social Engineering techniques
Featured Partners
Related Videos
 43:56
43:56Getting under the skin: The Social Engineering techniques
Mauro Verderosa
 57:47
57:47Cracking the Code: Decoding Anti-Bot Systems!
Fabien Vauchelles
 1:58:59
1:58:59Stranger Danger: Your Java Attack Surface Just Got Bigger
Vandana Verma Sehgal
 24:09
24:09Plants vs. Thieves: Automated Tests in the World of Web Security
Ramona Schwering
 37:36
37:36Walking into the era of Supply Chain Risks
Vandana Verma
 27:10
27:10Hack-Proof The Node.js runtime: The Mechanics and Defense of Path Traversal Attacks
Sonya Moisset
 1:00:19
1:00:19Cyber Sleuth: Finding Hidden Connections in Cyber Data
Jennifer Reif
 40:38
40:38How to Cause (or Prevent) a Massive Data Breach- Secure Coding and IDOR
Anna Bacher
Related Articles
View all articles



From learning to earning
Jobs that call for the skills explored in this talk.

{"@context":"https://schema.org/","@type":"JobPosting","title":"Penetration Tester
Integrity360
PHP
C++
Java
Unix
Ruby
+5




Penetration Tester
Anson McCade
Manchester, United Kingdom
£60K
C++
Python
Scripting (Bash/Python/Go/Ruby)

Offensive Security Tester Red Team
Client Server
Charing Cross, United Kingdom
Remote
£35-50K
C++
Java
Python


Defensive Security Engineer (IR)
Adevinta
Barcelona, Spain
Kubernetes
Agile Methodologies
Amazon Web Services (AWS)
